My server has been hacked and was sending lots of spam over the Internet. The first thing I did is shutdown postfix, close the outgoing port 25 and take the time to clean the website, the postfix queues, and to re-setup postfix completely.
I enabled lots of restrictions on the Postfix SMTPD, like forcing SASL authentification and TLS.
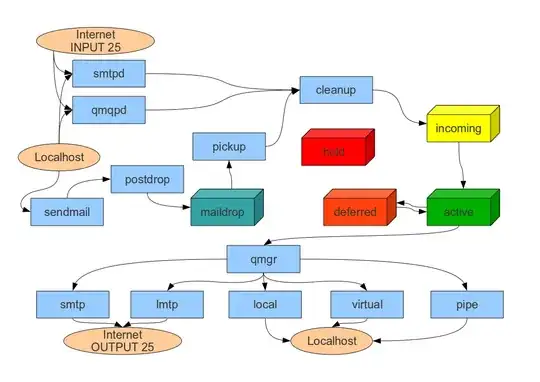
But I'm just thinking, PHP mail() function doesn't care about SMTPD, because it calls sendmail, whose emails end in the maildrop queue, and finally in the incoming queue (and bypass all of my SMTPD protections).
I made a small sketch of Postfix daemons and queues for myself, in order to understand better how it works.
I would like following setup:
- Prevent sendmail from delivering emails to outside recipients, but allow it to deliver emails to local users, and allow it to follow mappings in /etc/aliases even if it is an "ouside" mapping.
My aim is that at the end, users have no other choice than contact local SMTPD directly, thus forced to login thanks to my smtpd_client_restrictions = permit_sasl_authenticated, reject configuration.