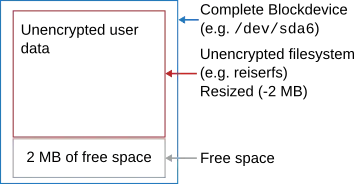
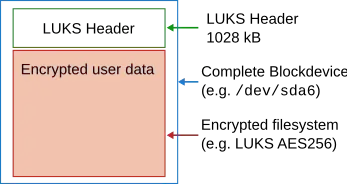
Tools are supposed to exist but I cannot offer a name or URL. But if you are not afraid :-) then it's not even difficult. All you have to do is read from the unencrypted device and write to the encrypted device. And you cannot use LUKS unless you resize the filesystem before to make it a bit smaller. And of course this does not work with the device being mounted (probably not even if it's mounted ro). The core function (without any protection against crashes) is this (and yeah, I just tried it successfully):
for((i=0;i<100;i++)); do
echo "Copying block with offset ${i} to tmpfs"
dd if=/dev/storage2/test of=/mnt/tmpfs/cryptoblock skip=$i bs=10M count=1 &>/dev/null
echo "Copying block with offset ${i} from tmpfs"
dd if=/mnt/tmpfs/cryptoblock of=/dev/mapper/crypt_test seek=$i bs=10M count=1
done
The obvious demand for improvment is: copy the blocks to a non-volatile medium instead and log their offset. In case of a crash you manually copy the block of the interrupted transaction and start the loop with the offset of the next block as start value.