I have a tcpdump (pcap) capture file and want to extract all domains. I do it with the following command:
strings capture_file | grep -oiE '([a-zA-Z0-9][a-zA-Z0-9-]{1,61}\.){1,}(\.?[a-zA-Z]{2,}){1,}' | sort -u > out
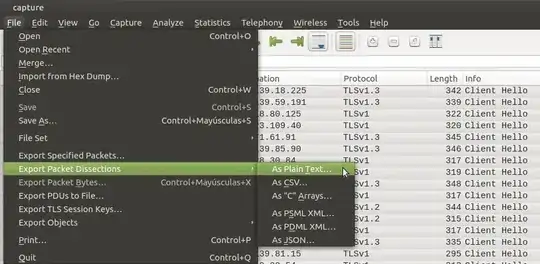
But I want to extract only those related to the string "Client Hello". Example in Wireshark:
Handshake Protocol: Client Hello
Server Name: example.com
Is there any way of doing this?