After an incorrect record was added to /etc/fstab, CentOS is, expectedly, failing to boot.
I've been looking around and found a lot of different solutions but I'm unable to resolve my issue.
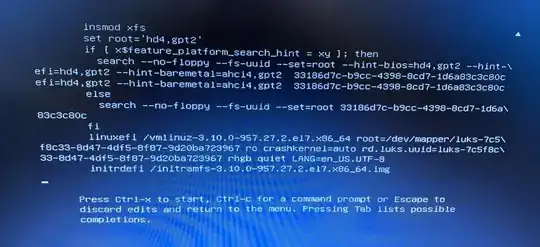
When editing the kernel file for CentOS, I press e, and I am presented with this file:
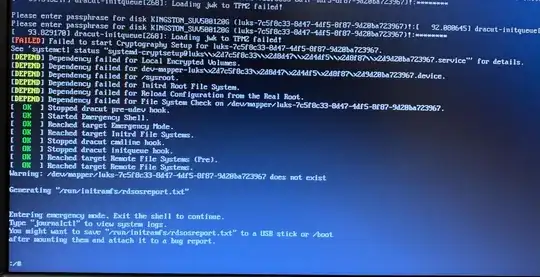
I've tried different combinations of adding init=/bin/bash or rw or single, etc. to the linuxefi line, but mostly I end up on a screen that prompts for a passphrase:
I don't have the passphrase for this, and I am looking for a password-less option of editing the bad /etc/fstab file.
If I enter an incorrect password three times, I'm entered into a version of emergency mode, however I can't edit /etc/fstab, only a file /etc/fstab.empty exists, which is, unsurprisingly, empty.
Edit: The following information is how we are installing CentOS in the first place, which I believe may indicate that we are encrypting the hard disk, which I think means that I am stuck...
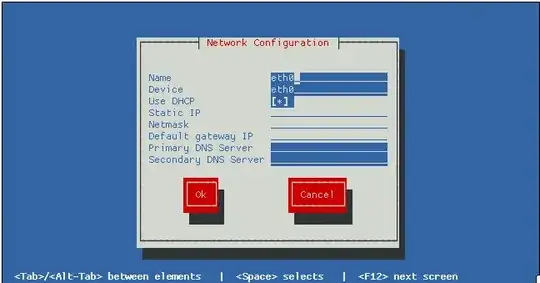
Using text mode:
# Secure Boot Mode:
part /boot/efi --fstype="efi" --size=200 --fsoptions="umask=0077,shortname=winnt"
part /boot --fstype="xfs" --size=200
part / --fstype="xfs" --grow --encrypted --passphrase=temppass
Later:
# --------------------------------------------------------------------------------------------------
# Setup HDD Encryption
# --------------------------------------------------------------------------------------------------
yum install -y clevis clevis-luks clevis-dracut
# Entries from previous installs can remain and cause problems:
luksmeta nuke -f -d /dev/sde3
# Move decyption to the TPM:
clevis luks bind -f -k- -d /dev/sde3 tpm2 '{"pcr_ids":"7"}' <<< temppass
echo -n temppass | cryptsetup luksRemoveKey /dev/sde3 -
dracut -f