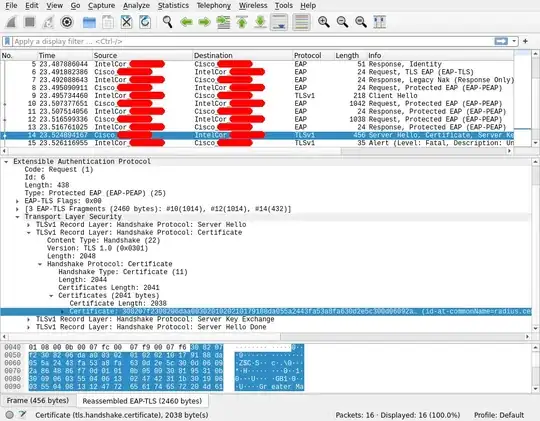
I have a work network which is an EAP enterprise WiFi network using PEAP and MSCHAPv2. I unfortunately don't have the CA certificate for the network, which presumably makes it trivial to harvest my credentials by spoofing the network.
Is there a way for me to fetch the CA presented by the WiFi network so I can set it as the CA certificate to prevent spoofing?
EDIT: According to Wikipedia on PEAP, the WiFi server uses a CA for signing its server-side certificate for trust:
A CA certificate must be used at each client to authenticate the server to each client before the client submits authentication credentials. If the CA certificate is not validated, in general it is trivial to introduce a fake Wireless Access Point which then allows gathering of MS-CHAPv2 handshakes.[9]
I need to get this CA certificate somehow from the server, as I'm sure it issues a certificate chain with the server public key certificate and the CA public key certificate. Presently it is configured without a CA certificate, allowing arbitrary spoofing: