I'm trying to debug an LDAPS connection from Ubuntu 14.04 to some sort of VIP. There are 6 nodes behind the VIP. The connection only succeeds "sometimes". A wireshark log shows the failing connections being issued TLSv1.2 Alerts "Fatal, Illegal Parameter" with a Content Type "Alert (21)" which apparently only means wireshark can't decrypt the alert record.
I don't have access to the server's private key so I cannot decrypt the wireshark session. I'm trying to get the server admin to do it. In the meantime, is there any way to find out what cipher is being settled on with the connection does work? I've tried ldapsearch -d 255 ... but it doesn't reveal anything about the cipher that I can see, so far.
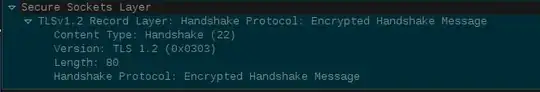
When the connection does succeed, The TLS record layer in wireshark says looks like this, if it's of any use: