1. DNS Zone Blacklist Generator
I came across this projects called dns-zone-blacklist which based on its description sounds like what you want.
This project generates a zone file for BIND, Dnsmasq and Unbound DNS servers using data from the StevenBlack/hosts project. The generated zone files can be used to block ads and malware for an entire network when used with a local DNS server.
To use this blacklist you simply do the following:
download
$ git clone https://github.com/oznu/dns-zone-blacklist.git
$ cd dns-zone-blacklist
install nodejs
$ npm install
build/compile blacklists
$ node build.js
Once built, you'll end up with 3 directories: ./bind, ./dnsmasq, and ./unbound. The resulting configuration file(s) for unbound will be located in the ./unbound directory.
$ ll unbound/
total 4852
-rw-rw-r-- 1 vagrant vagrant 3372150 Jul 16 00:15 unbound.blacklist
-rw-rw-r-- 1 vagrant vagrant 64 Jul 16 00:15 unbound.blacklist.checksum
-rw-rw-r-- 1 vagrant vagrant 1584122 Jul 16 00:15 unbound-nxdomain.blacklist
-rw-rw-r-- 1 vagrant vagrant 64 Jul 16 00:15 unbound-nxdomain.blacklist.checksum
You would then add these files to Unbound's /etc/unbound directory and restart.
2. DNSblacklist
Another option is DNSblacklist. You do a similar set of steps in pulling this down via git into your /etc/unbound directory, and configure it using the supplied unbound.conf file.
Within the Git repo is a directory, blackhole, that includes a shell script, run.sh. You simply run the script, run.sh, and then check the configuration files using unbound-checkconf. If all is good, simply restart Unbound.
3. Using Pi-Hole instead of Unbound
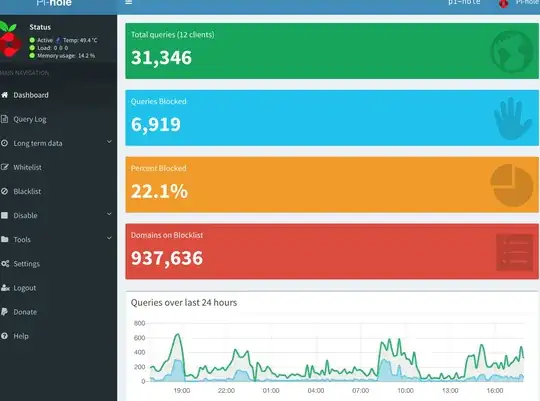
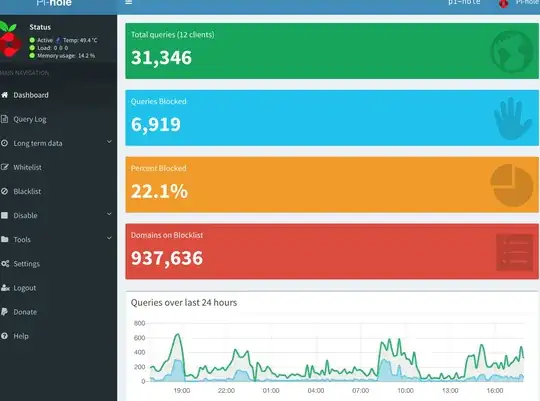
Just a tip but I've been using https://pi-hole.net/ for the last couple of months and really cannot recommend it enough for doing ad blocking at the DNS level. I run it on a ~$35 Raspberry Pi and have even added DHCP + all my internal DNS to it.
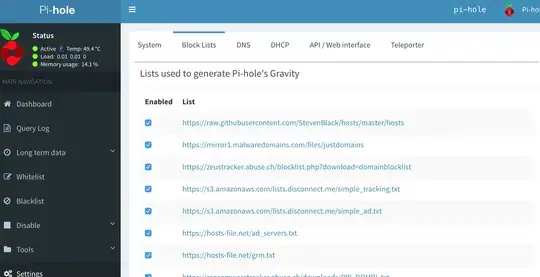
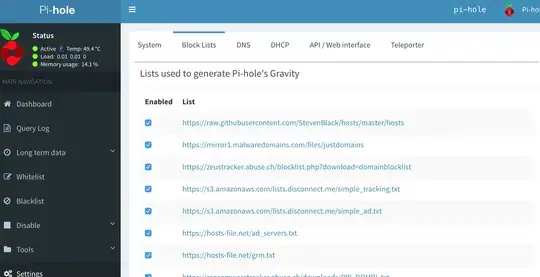
The web UI is very easy to navigate and you can add all the lists you want through the UI. Here I've added 50+ lists to my UI and have ~937K domains blocked.
The lists are getting added under this directory on the device:
$ ls /etc/pihole/
adlists.list list.20.www.joewein.net.domains list.3.s3.amazonaws.com.domains list.59.v.firebog.net.domains
auditlog.list list.21.raw.githubusercontent.com.domains list.40.v.firebog.net.domains list.5.hosts-file.net.domains
black.list list.22.hostsfile.org.domains list.41.raw.githubusercontent.com.domains list.60.v.firebog.net.domains
blacklist.txt list.23.someonewhocares.org.domains list.42.raw.githubusercontent.com.domains list.61.raw.githubusercontent.com.domains
dhcp.leases list.24.raw.githubusercontent.com.domains list.43.raw.githubusercontent.com.domains list.62.ransomwaretracker.abuse.ch.domains
GitHubVersions list.25.raw.githubusercontent.com.domains list.44.raw.githubusercontent.com.domains list.63.v.firebog.net.domains
gravity.list list.26.winhelp2002.mvps.org.domains list.45.raw.githubusercontent.com.domains list.64.raw.githubusercontent.com.domains
install.log list.27.hostsfile.mine.nu.domains list.46.raw.githubusercontent.com.domains list.65.zeustracker.abuse.ch.domains
lan.list list.28.v.firebog.net.domains list.47.raw.githubusercontent.com.domains list.66.raw.githubusercontent.com.domains
list.0.raw.githubusercontent.com.domains list.29.adblock.mahakala.is.domains list.48.github.com.domains list.6.hosts-file.net.domains
list.10.reddestdream.github.io.domains list.2.zeustracker.abuse.ch.domains list.49.raw.githubusercontent.com.domains list.7.ransomwaretracker.abuse.ch.domains
list.11.hosts-file.net.domains list.30.adaway.org.domains list.4.s3.amazonaws.com.domains list.8.v.firebog.net.domains
list.12.reddestdream.github.io.domains list.31.v.firebog.net.domains list.50.v.firebog.net.domains list.9.v.firebog.net.domains
list.13.raw.githubusercontent.com.domains list.32.s3.amazonaws.com.domains list.51.s3.amazonaws.com.domains list.preEventHorizon
list.14.raw.githubusercontent.com.domains list.33.hosts-file.net.domains list.52.mirror1.malwaredomains.com.domains localbranches
list.15.v.firebog.net.domains list.34.v.firebog.net.domains list.53.hosts-file.net.domains local.list
list.16.v.firebog.net.domains list.35.raw.githubusercontent.com.domains list.54.hosts-file.net.domains localversions
list.17.sysctl.org.domains list.36.pgl.yoyo.org.domains list.55.hosts-file.net.domains logrotate
list.18.raw.githubusercontent.com.domains list.37.raw.githubusercontent.com.domains list.56.mirror.cedia.org.ec.domains pihole-FTL.db
list.19.www.dshield.org.domains list.38.v.firebog.net.domains list.57.www.malwaredomainlist.com.domains setupVars.conf
list.1.mirror1.malwaredomains.com.domains list.39.v.firebog.net.domains list.58.bitbucket.org.domains whitelist.txt
Black lists
I started with The Big Blocklist Collection and followed links to collect all the blacklists that I ended up adding to my Pi-Hole device.
References