When SELinux is installed on a system are its rules enforced before or after the standard linux permissions? For example if a non-root linux user tries to write to a file with linux permission -rw------- root root will SELinux rules be checked first or will standard filesystem permissions apply and SELinux never invoked?
Asked
Active
Viewed 2,034 times
23
Gilles 'SO- stop being evil'
- 807,993
- 194
- 1,674
- 2,175
satur9nine
- 651
- 4
- 16
-
2SELinux is disabled in your example listing. – Michael Hampton Feb 01 '17 at 07:41
-
@MichaelHampton I don't think so? However, the `ls` command used for the example didn't include `-Z`, but the example output doesn't give me enough information to see if SElinux is on or off. If you're referring to the missing `+` in the bitmask, this is not SElinux but filesystem ACLs. – jornane Feb 01 '17 at 08:36
-
2@jornane I'm referring to the missing `.` in the listing. It appears if SELinux is enforcing or permissive, whether you use `-Z` or not. – Michael Hampton Feb 01 '17 at 08:57
-
Ah, I checked on a non-RHEL Linux machine. You're right, `.` doesn't appear there. Today I learned. :) – jornane Feb 01 '17 at 15:10
1 Answers
31
I see the terms to search for now are MAC and DAC. DAC is the standard permission system. MAC is the system used by SELinux.
The answer to quote one source is:
It is important to remember that SELinux policy rules are checked after DAC rules. SELinux policy rules are not used if DAC rules deny access first.
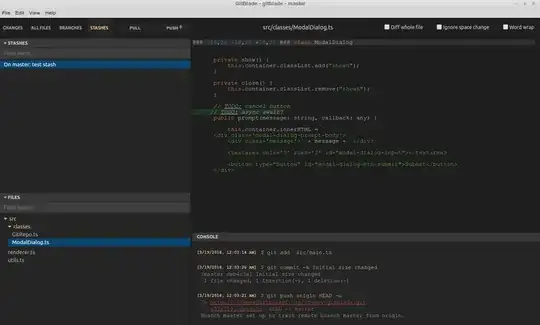
This diagram shows:
References:
https://selinuxproject.org/page/NB_MAC
https://www.centos.org/docs/5/html/Deployment_Guide-en-US/selg-overview.html
satur9nine
- 651
- 4
- 16