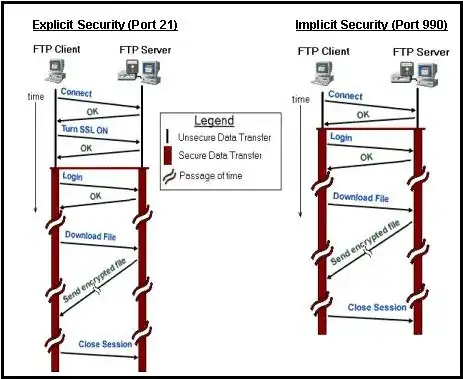
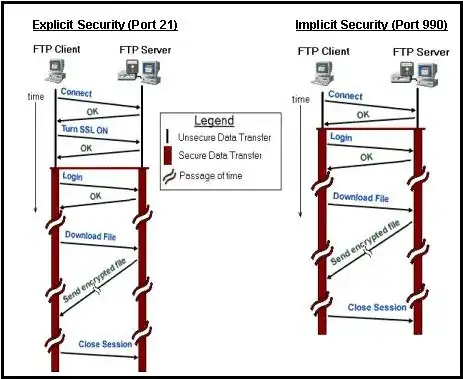
There are two ways in which an FTPS session can be established: explicit (also called FTPES) and implicit.
They both acomplish the same thing (FTP over SSL), but vary on how the connection is initiated.
Explicit: Client connects to the standard FTP port (21) with a regular FTP connection, and then a command is sent by the client requesting to upgrade the connection to SSL, allowing the connection to fallback to a regular FTP session if requested by the client.
Implicit: Client connects to the default port 990, and an SSL session is established as soon as the client connects to the server.
The entire session is encrypted and only SSL sessions are allowed.
Edit:
The diagram below (from: globalscape.com) nicely illustrates the differences:
As for which to choose, well this depends on your requirments.
See the two below excerpts:
Both Implicit and Explicit FTPS offer comparable levels of encryption
(assuming that with Explicit FTPS you choose the option to encrypt
both the data and control channels).
From a practical standpoint, Explicit FTPS offers some advantages that
make it a superior choice. For example:
It is the standard, supported version of FTPS and is more likely to be widely supported well into the future
It uses the same ports as plain FTP, so requires no additional firewall configuration (assuming your firewall is already configured
for plain FTP).
(Source: Robo-FTP web page:)
Implicit FTPS consumes a lot of network bandwidth and computational
resources because encryption happens in both the command and data
channels. In a scenario where a user wants to upload non-confidential
files to the FTPS server, an explicit FTPS connection would be used
instead of an implicit FTPS connection.
In Explicit FTPS, the client directly requests security from the FTPS
server. This is an optional request. If a client does not request
security, the FTPS server can either allow the client to continue in
unsecure mode or refuse or limit the connection.
Explicit FTPS can be used in scenarios where the requirement is to
secure only the command channel (which carries the commands and user
authentication,) and not the data channel (which carries
non-confidential FTP data). Port 21 is the default port used by the
FTP server to communicate with the client. This allows both unsecure
FTP and secure FTPS clients to connect to the FTPS server.
For organizations adhering to federal regulatory compliance standards,
implicit FTPS is recommended.
(Source: Serv-U web page)