TL;TR: FTP is a broken protocol and FTPS more so. Due to a combination of protocol design and encryption it plays very bad together with firewalls. Try to use SFTP (i.e. file transfer over SSH protocol) instead.
FTP consists of a control connection (usually port 21) and the data connections. Which ports are used by the data connections are dynamically exchanged within the control connection. In active mode the clients listens on IP/port given inside the PORT or EPRT command and the server connects to the client. In passive mode the server listens on IP/port given in response to the PASV or EPSV command and the client connects to the server.
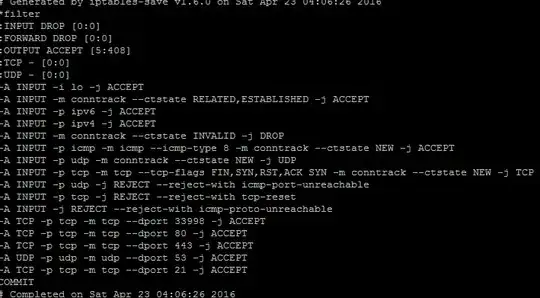
One way to deal with this kind of dynamic ports in a firewall configuration is to keep a wide range of ports open. This is obviously contradicting the idea of using a firewall to restrict the attack surface as much as possible. Thus most firewalls offer some "helpers" which inspect the control connection and find out which ports are used for the dynamic connections so that they can create matching packet filter rules on demand. With iptables this is done inside ip_conntrack_ftp. This is what you are trying now.
Unfortunately using such helpers means that the firewall must be able to read the traffic inside the control connection. If you don't use plain unencrypted FTP this is possible. But with FTP+TLS the control connection is encrypted and thus the helper is not able to extract the necessary information to open the ports on demand. In theory there is a way to deal with this by using TLS only for transferring the authorization part but then switch off encryption again (FTPS command CCC) but this would need to be supported and used by the client.
Thus if possible avoid FTP and FTPS and use SFTP instead. This is file transfer over the SSH protocol and uses only a single port which makes a restrictive firewall configuration easier.