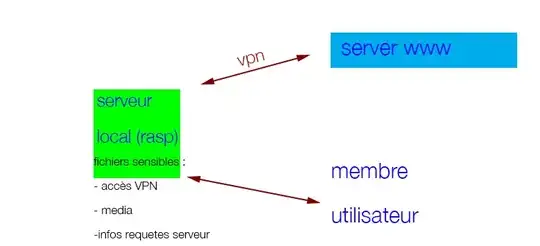
In your application, you want to protect at least:
- The actual media files obtained from the server
- The VPN keys that allow the Raspberry to connect to the VPN (otherwise an intruder need only extract that key, connect to the VPN themselves, and get the files)
You can encrypt only those things, or you can encrypt the entire root filesystem. Perhaps you might as well do the latter while you are at it.
You can use luks to encrypt the Raspberry's root filesystem. You can find instructions for setting up a Debian (and presumably Mint) system with encrypted root from many sources. Basically, you can do it from the installer before the system is installed. Converting a system after the fact is much more trouble because you have to:
- boot an alternate system
- mount the target root filesystem and copy its contents elsewhere (implies having spare storage)
- reformat the target root filesystem with luks
- copy everything back
- Add the new encrypted partition to
/etc/crypttab, adjust /etc/fstab
- With
chroot or similar, regenerate the target's initramfs so that it will have the ability to decrypt the root at boot.
A separate root filesystem and /boot filesystem is a must, so you should start with a system that already has that if you go with the conversion option. Converting an existing system to encrypted root is a bit of an expert procedure. I quickly found a tutorial but I haven't read it so I cannot vouch for it.
If the Raspberry must boot unattended on its own, then you are faced with the problem that whatever you do is insecure: the unit must be able to unlock its own decryption, which means that the keys will be accessible to a thief. Still, the mitigation you propose in your comment, which is to physically separate the key on different media, is not a bad compromise if you must go that route.
This other question covers how to make the system access its own decryption key at boot time in an automated fashion. Instead of a keyscript that just echos the passphase as proposed in that solution, you would create a short script that:
- mounts the physically separate media
- loads and outputs the passphrase from a file over there
- unmounts the separate media
That script would run from inside the initramfs. Untested: such a script could look something like this:
mkdir -p /mnt/key
mount /dev/disk/by-id/sd-card-whatever-the-device-name-is-part1 /mnt/key
cat /mnt/key/root-filesystem-key
umount /mnt/key
...and add a keyscript option in /etc/crypttab that names that script.