This is one that I've never really known how to do, and it's been nagging me from time to time for years. I've read all I could find, including all the answers here. None of them gives a real answer to the question. So please read carefully before flagging a duplicate; it is not.
dig, host, nslookup... none of them seems to be able to get what I'm after.
At most I can get pointers like ec2-xxx-xxx-xxx-xxx.us-east-2.compute.amazonaws.com.
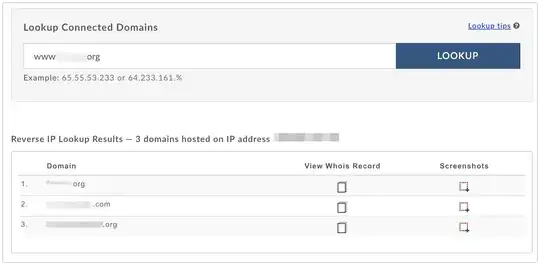
But if I use this online tool, I get exactly what I'm looking for: every domain that resolves to the IP address given (or a hostname). In this case, it's a freemium service, so it'll only list the first few, but it works. In the following image, I use three domains that I own and serve from a VPS. They are totally unrelated, but they all appear here:
What black magic are they using? How can we replicate it?