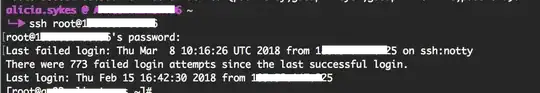
No it's not normal, but it has become commonplace courtesy of poor defaults, uninformed users, hackers and security testers.
If you've got good and secure passwords or use keys, and plenty of space for your log files, then there's nothing to worry about.
A great solution to clean this up though, is to set up automation so that the owner of the originating network (the source) gets a notification that this is being done from his network, so that they can act fast to block it, and clean it up. Most of this traffic is a sign of malware on your network blocking machines or users doing this will protect other users who might fall victim to potential exploits or nefarious users.
All the nefarious users running botnets and trying to take over your devices, will of course downvote this.